The Importance Of Server Hardening
If you are working in any field, at least you have ever heard about the term “Server”. Especially in the IT field, you must know how vital servers are for the business because servers are places for businesses [
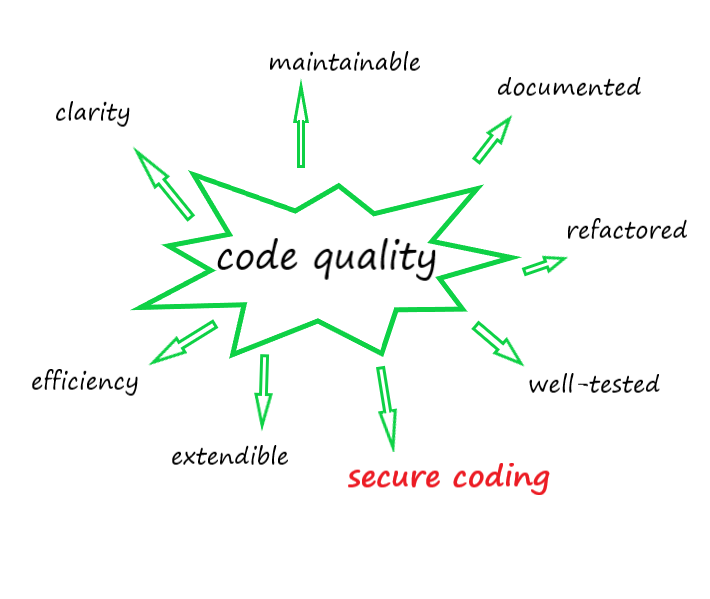
To Build Your Code Quality (Chapter A): Secure Coding (Part 2)
In the previous part, we have mentioned to threats from Input Validation, Man-In-Middle, Session Management, Error Handling [
To Build Your Code Quality (Chapter A): Secure Coding (Part 1)
From the roots of issues Code quality’s always a matter of software engineering. It’s hard to measure the level of code quality and even to define it. As a result of searching [
[Mindmap] Risk-based Testing Overview by MeU Solutions
What is Risk-based testing Risk-based testing (RBT) is a type of software testing that functions as an organizational principle used to prioritize the tests of features and functions in software, based on the risk of failure, the function of [
[Video] OWASP – Insecure Direct Object References – Have you known it intimately?
Insecure Direct Object References (IDOR) is referenced in element A4 of OWASP top 10 in 2013 edition. It’s no longer in top ten as an individual but was merged into A5 – Broken Access Control in top 10 OWASP [
[Video] CSRF (Cross Site Request Forgery) Attacks tutorial & Exploit CSRF in DVWA (Low, High Level)
A successful CSRF attack can be devastating for both the business and user. It can result in damaged client relationships, unauthorized fund transfers changed passwords and data theft—including stolen [
[Video] XSS – Cross Site Scripting – More dangerous than you think!
Watch this video tutorial -- a video from MEU SOLUTIONS, if you want to learn about XSS (Cross Site Scripting) exploit, It's more dangerous than you think. You will also learn how to prevent this attack. Remember to Like, [
[Video] OWASP Top 10 series (Part 1): SQL Injection exploitation- step by step
Penetration tester team at MeU [