Security Testing Solutions
Secure Your Data. Secure Your Business.
Straightforward Solutions to Complex Security Issues.
Application Security Testing is a critical component of application security and the cornerstone of any software security initiative. MeU Solutions offers security testing solutions/penetration testing solutions to ensure your application is secured from any vulnerabilities and met the stated security requirements like confidentiality, authorization, authentication, availability, and integrity. We apply the OWASP (Open Web Security Project) guidelines along with HIPAA Standards.
Our Practices
Our people has demonstrated their capability of security testing with various applications, especially, with proven records in security testing/ penetration testing for government projects – will be a good choice for your application security testing.
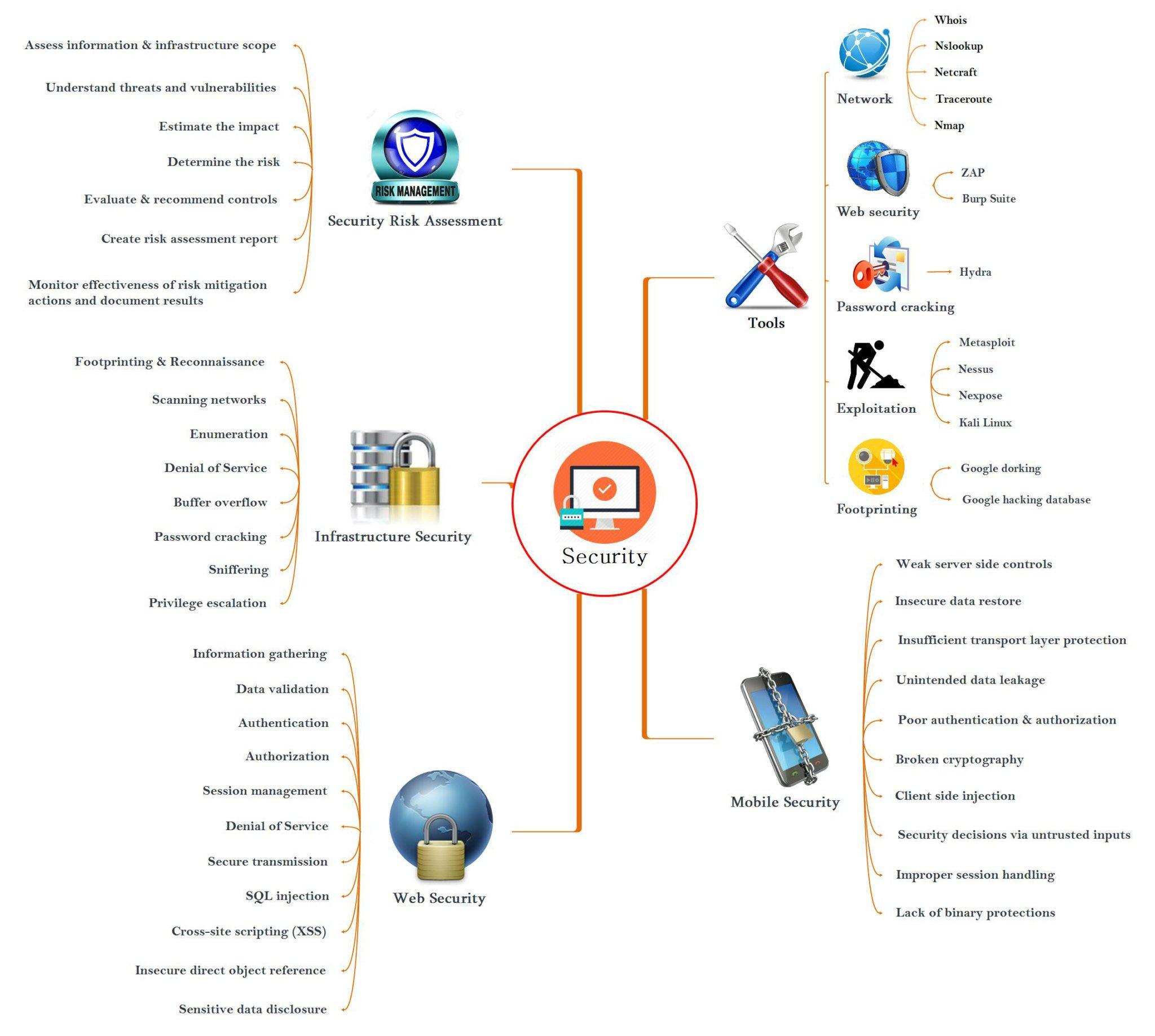
Our Tools
- Burp Suite
- Acunetix
- Cenzic Hailstorm
- HP Web Inspect
- Metasploit
- Nessus
- ….
If you don’t see the software testing solution you’re looking for, don’t worry, please feels free to send us a request for it.


Our People
Our testing professionals with multiple skills who are good at both test approaches, techniques, tools, and an excellent mindset.
- A pool of trained CEH (Certified Ethical Hackers)
- Proven records with testing for government’s system with complex & high-security requirements (check out our story)
- Conformance with international standards including OWASP, HIPAA
- Familiar with tools Burp Suite, Acunetix, Cenzic Hailstorm, HP Web Inspect, …
Safeguard Your Business
with our Security Testing Tools & Security Testing Solutions.
Want to learn more about how our QA and testing services can safeguard your brand? Contact us to find out how we can improve your QA ROI.
Relate Articles
-
What are Test Oracles and Test Heuristics
In the world of testing, we frequently hear the words Test Heuristics and Test Oracles, however what are they and how we can execute them into our day by day testing activities? Test oracle is a mechanism that determines [
-
Improve Collaboration Between Tech Team Members
Many organizations today find it increasingly challenging to raise or maintain team collaboration across the workplace. And yes, team collaboration is the cornerstone [
-
Why I Record All My Test Sessions – A picture is worth a thousand words
In communication, how do you convince others and get their trust? Of course, every word is convincing when it is right, and there must be clear evidence of what you want [
-
Check out Our New Case Study: How We Helped a Multi-channel Bill Payment Service Provider Improve Software Quality
At MeU Solutions, we help clients gain valuable insights about [





