One Secure
1Secure is a Security Testing As Services which is designed by MeU Solutions.
Our service is to propose a systematic approach to assessments of your infrastructure and your web application is ideal for uncovering any risks you might be unaware of.
Our security assessment includes some form of penetration testing, but it takes a more formal and systematic approach and provides a comprehensive view of where all the exploitable vulnerabilities are, and what actions should be taken to remediate them.

OWASP Standards
OWASP Standards which provides a basis for testing web application technical security controls and also provides developers with a list of requirements for secure development.
By applying these standards, we establish a level of confidence in the security of your Web Applications. Our assessment is a very valuable exercise for decision-makers, presenting them with a point-in-time view of your security posture.
Our Deliverables
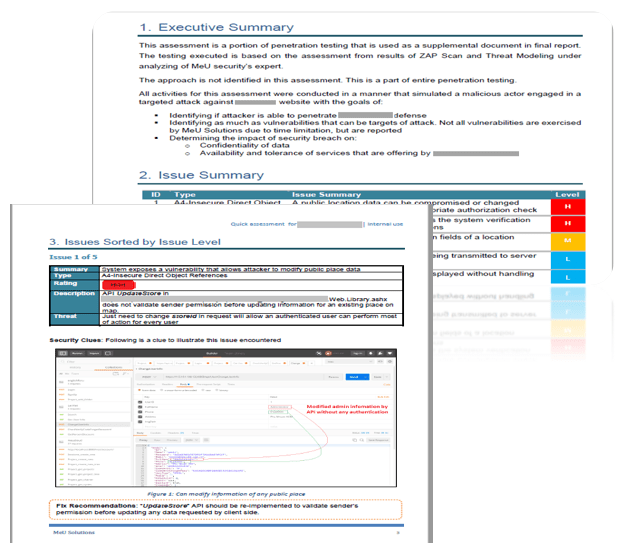
We strive to focus our effort on the value of our service and findings – and provide you with the information that you need to fix any identified vulnerabilities. Our Service with deliverable as follows:
- Threat Scan Result and Analysis
- Final Report
- Statement of Scope
- Statement of Methodology
- Findings
- Tools and uses
- Fix Recommendations
- Risk Assessment
- Tools and Standards
- ZAP (Zed Attack Project)
- Burp Suite
- Qualys SSL Lab
- Nessus
- Nexpose
- Metasploit
- Kali Linux
- Google dorking

Our Practices
Our testing professionals with multiple skills who are good at both test approaches, techniques, tools, and an excellent mindset.
- OWASP Top 10: The OWASP Top 10 is a powerful awareness document for web application security. It represents a broad consensus about the most critical security risks to web applications.
- OWASP Mobile Top 10: “The Big Picture” is all about understanding the top 10 mobile security risks we face on the web today in an easily consumable, well-structured fashion that aligns to the number one industry standard on the topic today.
- SANS Top 25: The 2011 CWE/SANS Top 25 Most Dangerous Software Errors is a list of the most widespread and critical errors that can lead to serious vulnerabilities in software. They are often easy to find, and easy to exploit. They are dangerous because they will frequently allow attackers to completely take over the software, steal data, or prevent the software from working at all.

